http://indianexpress.com/article/india/ ... k-2875564/
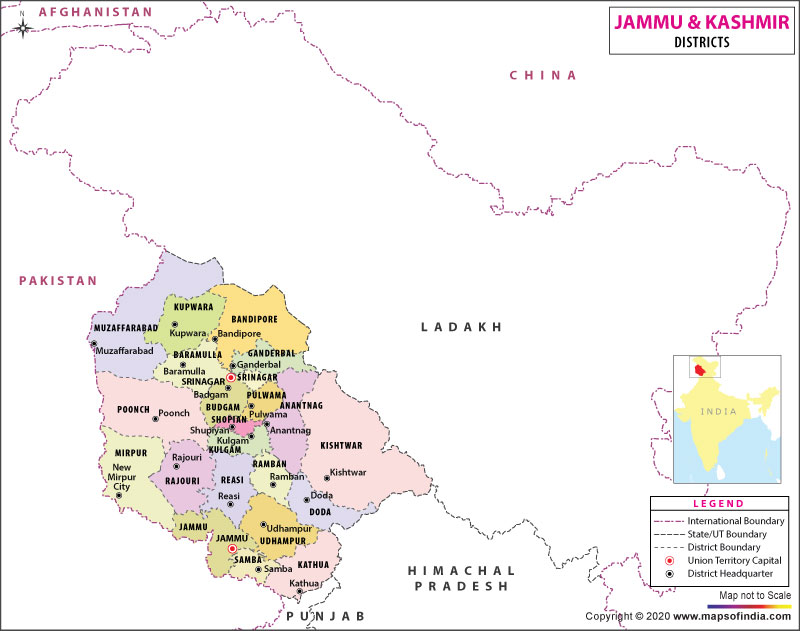
At least eight CRPF personnel were killed after suspected militants opened fire on a bus carrying the jawans in Pampore, Jammu-Kashmir. Two terrorists were also gunned down in the return fire by the paramilitary force.
“Two terrorists were killed, we’ve lost 5 jawans and 20 injured. The injured were admitted in a hospital,” said Rajesh Yadav, CRPF commandant.
However, three more jawans succumbed to their injuries at an Army Hospital.
READ: J&K: Two militants killed by security forces in Baramulla
The CRPF jawans were reportedly ambushed by the militants while returning to their base after a practice session at a nearby firing range. The operation is currently underway as two more militants are believed to be hiding in the vicinity of the scene of encounter, he said.
GALLERY | Pampore: At least 8 CRPF jawans killed in militant attack on convoy
MoS Kiren Rijiju said that the terrorists fled from the spot using a getaway vehicle.
“The one’s (terrorists) who were in car fled from the spot, However, jawans were able to kill 2, necessary action being taken,” said Rijiju.
Home Minister Rajnath Singh was reportedly briefed on the Pampore attack. The DG of the paramilitary force and other senior officials are expected to reach Pampore tomorrow and take stock of the situation.