The official website of the Pakistan People's Party (PPP) was defaced Wednesday by a team of Indian hackers, slamming PPP patron-in-chief Bilawal Bhutto-Zardari for his recent statement on Kashmir.
A group calling themselves the 'Indian Hackers Online Squad' replaced the website's homepage with messages ridiculing Bilawal for his comments, and claiming that “will never get Kashmir”.
“To Citizens of Pakistan, Pakistan's Army, Pakistan Peoples Party and Specially Mr. Bilawal Bhutto . Without any Violence Let Me tell you that Pakistan will never Get Kashmir. This is the Truth. You Have to Accept it,” said the message left by the hackers on the PPP official website.
Indian Cyber Warfare Discussion
Re: Indian Cyber Warfare Discussion
Indian hackers deface PPP website
-
member_28797
- BRFite
- Posts: 188
- Joined: 11 Aug 2016 06:14
Re: Indian Cyber Warfare Discussion
This doesn't exactly come under cyber warfare. This team wasn't sponsored by Indian govt. but good fun nonetheless.
Re: Indian Cyber Warfare Discussion
Under maintenance now!chaanakya wrote:http://www.pressclubofindia.org website was hacked by some baki hackers.
Still showing hacked page.
-
Ranjani Brow
Re: Indian Cyber Warfare Discussion
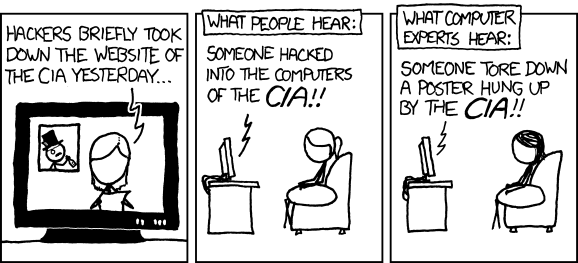
relevant xkcdchaanakya wrote:http://www.pressclubofindia.org website was hacked by some baki hackers.
Still showing hacked page.
Re: Indian Cyber Warfare Discussion
State of awareness about cyber security is quiet lackluster in our country.
Mode ji's older wabsite at nare****modi.in which was made in wordpress, used to display mysql hostname, username, password, whenever you would fill the request an appointment form.
I notified a concerned person but got no reply. I was quiet tempted to twit the screenshot, but avoided that out of sheer respect towards the man and pm.
The old site is now replaced with new one, hope they don't have new holes and have changed the mysql username and password
But cos of this crap, I didnt get appointment with pm
Mode ji's older wabsite at nare****modi.in which was made in wordpress, used to display mysql hostname, username, password, whenever you would fill the request an appointment form.
I notified a concerned person but got no reply. I was quiet tempted to twit the screenshot, but avoided that out of sheer respect towards the man and pm.
The old site is now replaced with new one, hope they don't have new holes and have changed the mysql username and password
But cos of this crap, I didnt get appointment with pm
-
member_28638
- BRFite
- Posts: 211
- Joined: 11 Aug 2016 06:14
Re: Indian Cyber Warfare Discussion
Introduction to Cyber Security Course
https://www.futurelearn.com/courses/int ... r-security
Starts 13th October
https://www.futurelearn.com/courses/int ... r-security
Starts 13th October
-
Mukesh.Kumar
- BRFite
- Posts: 1410
- Joined: 06 Dec 2009 14:09
Re: Indian Cyber Warfare Discussion
IAF sounds alert over Chinese cell phones
IAF is also believed to have alerted all its Commands and Squadrons and suggested that air force officers and their families should refrain from using Chinese mobile devices.
..........
According to New Indian Express, the latest IAF alert note reads, “F-secure, a leading security solution company, recently carried out a test of Xiaomi Redmi 1s, the company’s budget smartphone, and found that the phone was forwarding carrier name, phone number, IMEI (the device identifier) plus numbers from address book and text messages back to Beijing.........
IAF is also believed to have alerted all its Commands and Squadrons and suggested that air force officers and their families should refrain from using Chinese mobile devices.
..........
According to New Indian Express, the latest IAF alert note reads, “F-secure, a leading security solution company, recently carried out a test of Xiaomi Redmi 1s, the company’s budget smartphone, and found that the phone was forwarding carrier name, phone number, IMEI (the device identifier) plus numbers from address book and text messages back to Beijing.........
Re: Indian Cyber Warfare Discussion
Prime Ministers' addresses at the combined commanders conferences are generally mundane affairs, that typically steer clear of detail. At the last combined commanders' conference last November, then Prime Minister Manmohan Singh spoke of managing military budgets in times of economic downturn and civil-military balance. Modi's speech, however, articulated a vision which could instantly translate into instant deliverables on the ground.
He may have, for instance, tacitly approved a long- pending demand of the armed forces for the creation of three new commands: a cyber command, a special forces command and a space command. Modi noted "beyond the immediate, we are facing a future where security challenges will be less predictable; situations will evolve and change swiftly; and, technological changes will make responses more difficult to keep pace with.
"The threats may be known," Modi said, "but the enemy may be invisible. Domination of cyber space will become increasingly important. Control of space may become as critical as that of land, air and sea."
He asked the services to give serious thought to upgrade technological skills for effective "projection of power" by men. "When we speak of Digital India, we would also like to see a Digital Armed Force," he said.
The most important task, the PM observed, was to 'transform our armed forces'. He called for increased jointness and urged the three wings of the Services to work as a team all the way from the lowest levels of the Services to the top. He suggested a number of practical steps to achieve that goal.
Read more at: http://indiatoday.intoday.in/story/pm-m ... 96331.html
Re: Indian Cyber Warfare Discussion
Xiaomi Responds to Indian Air Force Security Concerns Over ‘Spying’Mukesh.Kumar wrote:IAF sounds alert over Chinese cell phones
IAF is also believed to have alerted all its Commands and Squadrons and suggested that air force officers and their families should refrain from using Chinese mobile devices.
..........
According to New Indian Express, the latest IAF alert note reads, “F-secure, a leading security solution company, recently carried out a test of Xiaomi Redmi 1s, the company’s budget smartphone, and found that the phone was forwarding carrier name, phone number, IMEI (the device identifier) plus numbers from address book and text messages back to Beijing.........
By Melissa Bailey
Link: http://www.androidheadlines.com/page/2
After the Indian Air Force (IAF) issued a circular to its 175, 000 employees that the Chinese smartphone manufacturer Xiaomi was a security threat, Xiaomi was forced to clarify the issue. In fact, the IAF told its staff that Xiaomi smartphones should not be used by themselves or members of their families due to suspicions that the company is using its manufactured phones to spy on users on the Chinese government’s behalf.
Xiaomi offers an opt-in secure internet service, which is optional, so users can turn the service on and off whenever they like. The company also provides access to Mi Cloud that allows users to back up and sync their data and information on a cloud. Further, users have access to a cloud messaging service that allows free text messaging between other Mi devices. Despite rumors that all the data is collected by the Chinese government, Xiaomi states that it does not collect any data associated with the services it provides, such as Mi Cloud and the Xiaomi Cloud Messaging service, unless the user provides explicit consent by switching on corresponding services.
In its defence, Xiaomi also stated that it uses encryption and has high security standards including the AES-128 standard to protect its users’ data. In an official Xiaomi press release the company stated: “We believe the advisory circular issued by IAF is based on events about 3 months back. It refers to the F-Secure test done on the Redmi 1S in July 2014 about the activation of our Cloud Messaging service (which enables users to send text messages for free, similar to other popular messaging services).”
While not denying any spy action, the company has previously provided us with information including a statement that Xiaomi does not collect any information without user permission. As with other telecommunications providers, Xiaomi is said to have extremely strict access controls with multiple authorizations for access to any of its users’ personal data. In fact, Xiaomi is migrating international user data outside of China. The data will be moved in several phases to Amazon Inc servers in the United States and data centres in Singapore. While its aggressive growth outside of China has brought scrutiny such as the statement provided to the IAF, the company still intends on expanding further. After yet another security issue for the previously Chinese-only company, we will be interested to see how well Xiaomi does ensuring the security of its users.
Re: Indian Cyber Warfare Discussion
Good going by GoI:
Rs 1,000 cr set aside for cyber shield
http://www.business-standard.com/articl ... 377_1.html
Rs 1,000 cr set aside for cyber shield
http://www.business-standard.com/articl ... 377_1.html
Re: Indian Cyber Warfare Discussion
Regin: Top-tier espionage tool enables stealthy surveillance
From the article :
An advanced piece of malware, known as Regin, has been used in systematic spying campaigns against a range of international targets since at least 2008. A back door-type Trojan, Regin is a complex piece of malware whose structure displays a degree of technical competence rarely seen.
Customizable with an extensive range of capabilities depending on the target, it provides its controllers with a powerful framework for mass surveillance and has been used in spying operations against government organizations, infrastructure operators, businesses, researchers, and private individuals.
It is likely that its development took months, if not years, to complete and its authors have gone to great lengths to cover its tracks
Its capabilities and the level of resources behind Regin indicate that it is one of the main cyberespionage tools used by a nation state.
Infections are also geographically diverse, having been identified in mainly in ten different countries.
Primary targets were Russia (28%), Saudi Arabia(24%) and targets in India(5%)
From the article :
An advanced piece of malware, known as Regin, has been used in systematic spying campaigns against a range of international targets since at least 2008. A back door-type Trojan, Regin is a complex piece of malware whose structure displays a degree of technical competence rarely seen.
Customizable with an extensive range of capabilities depending on the target, it provides its controllers with a powerful framework for mass surveillance and has been used in spying operations against government organizations, infrastructure operators, businesses, researchers, and private individuals.
It is likely that its development took months, if not years, to complete and its authors have gone to great lengths to cover its tracks
Its capabilities and the level of resources behind Regin indicate that it is one of the main cyberespionage tools used by a nation state.
Infections are also geographically diverse, having been identified in mainly in ten different countries.
Primary targets were Russia (28%), Saudi Arabia(24%) and targets in India(5%)
Re: Indian Cyber Warfare Discussion
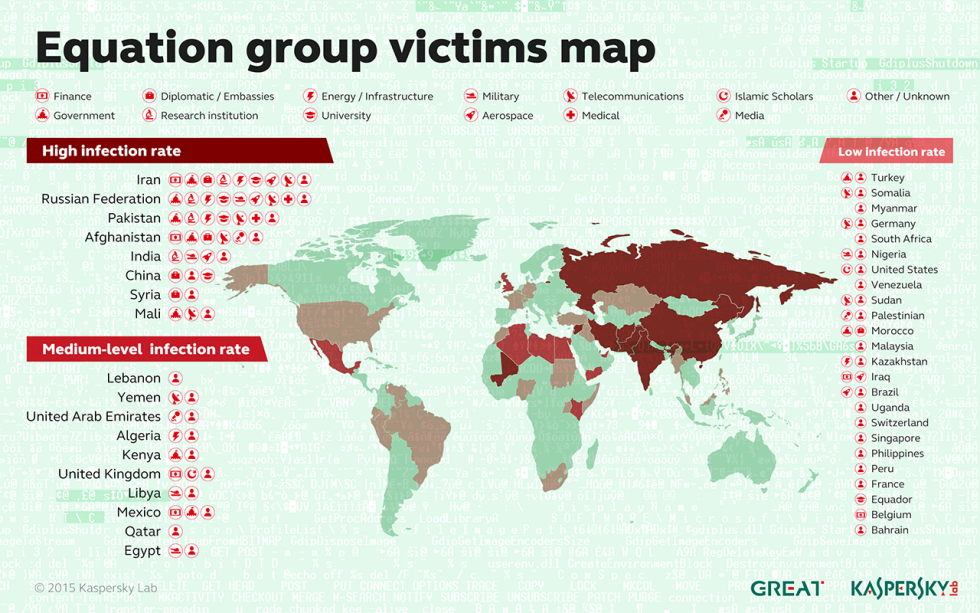
Equation Group: NSA-linked spying team have software to hack into any computer
http://www.independent.co.uk/life-style ... 51579.htmlThe US security services have developed software that has enabled it to spy on home computers almost anywhere in the world.
Russian researchers at Kaspersky Lab have claimed that the software gave those behind it, thought to be the US National Security Agency, the power to listen in on the majority of the world’s computers.
It could be installed on practically any of the world's most common hard drives and spy on the computer while going undetected.
It was used to break in to government and other important institutions in 30 countries across the world, they claim.
Re: Indian Cyber Warfare Discussion
Its a good thing that army and air force are developing their own cellular networks. This article states some cellular operators were affected.
https://firstlook.org/theintercept/2015 ... sim-heist/
https://firstlook.org/theintercept/2015 ... sim-heist/
Re: Indian Cyber Warfare Discussion
^^^ Thank You nmadhav ji, that is good link with a lot of details.
The AFCell or the secure IAF only Cell network has been rolled out. The AFNet and AFCell is a totally secure thing and is independent of the Civil use mobile and net services. One will not access Google from AFNet and if some smart guy tries, I have been informed that a minimum of Court Martial would be initiated.
AFCell comes with its own handset and its loss will cause action initiated like loss of Identity Card. I did not see any SIMs in use for AFCell and nor was I told of any SIM card. It was good to see the developments and IAF guys are happy. So far it has been rolled out up to SNCO levels (not sure).
The AFCell or the secure IAF only Cell network has been rolled out. The AFNet and AFCell is a totally secure thing and is independent of the Civil use mobile and net services. One will not access Google from AFNet and if some smart guy tries, I have been informed that a minimum of Court Martial would be initiated.
AFCell comes with its own handset and its loss will cause action initiated like loss of Identity Card. I did not see any SIMs in use for AFCell and nor was I told of any SIM card. It was good to see the developments and IAF guys are happy. So far it has been rolled out up to SNCO levels (not sure).
Re: Indian Cyber Warfare Discussion
Welcome, far-sighted move by PM & NSA.
Gulshan Rai becomes first chief of new Cyber Security post
Gulshan Rai becomes first chief of new Cyber Security post
BENGALURU: The Narendra Modi government has created a cyber-security chief's position under the Prime Minister's Office and has appointed Gulshan Rai, said a top official in the IT ministry.
Rai, who has been heading the computer emergency response team at the department of electronics and information technology (DeitY), will now take charge as special secretary for cyber security, people familiar with the development told ET.
Rai has been working since 1998 in the area of evolving legal framework to address issues arising out of cyberspace. He is also expected to head the national cyber coordination centre (NCCC) that the government is also setting up with a budget of Rs 1,000 crore. He was for a long time tipped to become the first national cyber security coordinator. Rai couldn't be reached for comments. DeitY has already posted a vacancy for the post of director general for Indian computer emergency response team.
Cyber security is fast becoming a nightmare for the government even as its Digital India initiative will increase the relevance of the internet and expose the country to large cyber-attacks.
Re: Indian Cyber Warfare Discussion
Pakistani cybersecurity firm stealing Indian bureaucrats’ data: FireEye
BENGALURU: A Pakistani cybersecurity firm with close ties to Islamabad has been found stealing information from Indian government and defence establishments, according to a two-year investigation by a US-based IT security firm.
The Pakistani company targeted Indian establishments using leased US hosting services, the US security firm, FireEye, said, the findings revealing that India remains a vulnerable target for cyberattacks even after documents leaked by whistleblower Edward Snowden exposed widespread spying on the country by the US National Security Agency.
While FireEye claimed the cyberattacks by the Pakistani firm were still active, the Indian government denied any knowledge of this. "It is incorrect. We have only seen cases of website hacking. However, they hold only public data," said Dr Gulshan Rai, director-general of the Indian Computer Emergency Response Team, or ICert, and who will shortly take charge as the country's first cybersecurity chief.
A senior Indian intelligence official confirmed Indian establishments were targets of cyberspying, but said the attackers could not be traced. "We have seen many such attacks targeting Indian government and defence establishments coming from different parts of the world, but in cyberspace it is very hard to ascertain the actual source of an attack."
According to FireEye, an Islamabad-based IT security firm called Tranchulas, which claims to have helped prepare the Pakistani government for cyberwarfare, bombarded officials in Indian government organizations with emails containing malicious software, or malware. The firm used 'Sarabjit Singh', Devyani Khobragade', 'Salary hikes for government employees' and other terms in the subject line of the emails to lure officials into opening attachments containing the malware, which would then infect the computers and collect an assortment of data that it would send to the cyberattacker.
"They are essentially penetrating Indian government accounts to find out what the Indian government is up to," Manish Gupta, senior vice president at FireEye said. "They are also targeting defence organizations. Some of the things that could be important to them could be what kind of weapons does India have, where are these weapons deployed, how many people are deployed in these regions, what is the organization structure, are there any military exercises planned."
Tranchulas CEO Zubair Khan, in an email response neither confirmed nor denied the involvement of his firm in the cyberespionage. "We've had no contact with (FireEye) so I have no idea about their motivations vis-a-vis their reporting on us. Clearly, they are one of the best security research companies out there and we respect their talents in this regard."
Khan said his company offers both government and private clients a special service, called the offensive cyberinitiative "to help select customers build sustainable strategies for cyberwarfare and cyberdefense that will keep them relevant in the information age."
The malware identified by FireEye has been active since early 2013 with the name of a Tranchulas employee, Umair Aziz, in its code. FireEye said that after it confronted Khan over this issue in July 2013, different variants of the malware with modified names have surfaced.
"Once we confronted Tranchulas, the malware was modified and all references to the company were removed and replaced with some strings with Cert-In (Indian computer emergency response team) to masquerade themselves and show that the attacks were being carried out by Indian Cert," said Michael Oppenheim, a threat intelligence analyst at FireEye who discovered the malware.
Tranchulas exclusively used VPSNOC, a Pakistan-based virtual private server service provider, which leased US hosting services to control phases of the attack, Oppenheim said. The senior Indian intelligence official mentioned earlier in the story said it was common for cyberattackers to use servers sublocated in a different country to avoid detection.
India has been trying to improve its cyberdefence capabilities in response to an increasing number of attacks, including by the United States, as revealed by the Snowden leaks. Earlier this month, prime minister Narendra Modi called upon the Indian IT Industry to focus on meeting the global challenge of cybersecurity. Cyberattacks on Indian websites have increased nearly five times in the past four years. Until mid-2014, more than 60,000 incidents were recorded by the ICert.
"India's data is in great demand across the world. It has been snooped across the continents but what is snooped is very important. What Pak agencies claim they snoop many a times is of far less importance as they end up in snooping data which has never traversed any physical form," said Prashant Mali, an advocated and independent cybercrime expert in Mumbai. But "India lacks concerted and coordinated efforts between all central agencies in managing these attacks," he said. "One umbrella organization to defend the cyberboundaries of India is the need of the hour."
Re: Indian Cyber Warfare Discussion
New Zealand Herald based on documents leaked by Edward Snowden reveals that New Zealand’s electronic eavesdropping agency, Government Communications Security Bureau (GCSB), has been spying on India as part of the “Five Eyes” Anglo-Saxon spying alliance led by the US and consisting UK, Canada and Australia besides New Zealand:
Snowden revelations: NZ's spy reach stretches across globe
Extract:
Snowden revelations: NZ's spy reach stretches across globe
Extract:
The NSA profile of the GCSB reveals the New Zealand organisation is running spying operations against 20 or more countries, including friendly nations and trading partners.
The eavesdropping stretches from India and Iran in Asia to isolated scientific bases in Antarctica. These countries are listed in the NSA report in a section headed "What Partner Provides to NSA".
The NSA officer's review said the GCSB "continues to be especially helpful in its ability to provide NSA ready access to areas and countries ... difficult for the US to access".
It said the "GCSB provides collection on China, Japanese/North Korean/Vietnamese/South American diplomatic communications, South Pacific island nations, Pakistan, India, Iran and Antarctica".
"Collection" means the GCSB conducts active surveillance on these countries and territories.
Re: Indian Cyber Warfare Discussion
http://economictimes.indiatimes.com/new ... 188880.cms
How Chinese hackers snooped on Indian defence agencies for over 10 years
excerpts
How Chinese hackers snooped on Indian defence agencies for over 10 years
excerpts
A Singapore based firm has uncovered a large scale cyber espionage network that is says is linked to the Chinese Government. The network has been active for 10 years in the region and targets India in particular by infecting computer systems of key, selected individuals and organisations. Terming it the APT30, Singapore firm FireEye says that the infection is specially targeted at Indian military, aerospace and maritime sector. What is interesting is that Singapore researches have uncovered the modus operandi of the spying network that uses decoy documents that users would
download or read in their emails or online. The decoy documents contain a bug that can transmit data and information from the infection computer system back to servers in China. The bug can even hide in documents and infect secure computers not connected to a network.
The Decoy documents are specially tailored to meet the interests of individuals or organisations to be targeted - these include government agencies, private industry and media groups. Chinese hackers used decoy documents on Indian
military movements in the South China sea, papers on the indigenous aircraft carrier under construction in Kochi, incidents on the China border and relations with Nepal
Re: Indian Cyber Warfare Discussion
http://www.rt.com/op-edge/310691-cyber- ... gislation/
The recent cyber-hacking into control of US cars with a recall of over a million+ is indicative of the seriousness of the issue.The missing MH aircraft that disappeared into thin air had one conspiracy theory that the aircraft's controls were deliberately hacked into by US intel/unknowns and flown to an unknown destination.'Frontline of the battle is not tanks or planes – it's cyberwarfare'
Annie Machon is a former intelligence officer for MI5, the UK Security Service, who resigned in the late 1990s to blow the whistle on the spies’ incompetence and crimes with her ex-partner, David Shayler. Drawing on her varied experiences, she is now a public speaker, writer, media pundit, international tour and event organiser, political campaigner, and PR consultant. She is also now the Director of LEAP, Europe. She has a rare perspective both on the inner workings of governments, intelligence agencies and the media, as well as the wider implications for the need for increased openness and accountability in both public and private sectors.
Published time: 24 Jul, 2015
People underestimate what cyberwarfare can do, but as the infrastructure of all our countries is run over the internet now, an attack on them could make society collapse within days, says Annie Machon, former MI5 agent.
Germany passed legislation which requires over 2,000 essential service providers to implement new minimum information security standards. If they fail to do so within two years they are going to face fines of up to €100,000.
READ MORE: Germany passes strict cyber-security law to protect ‘critical infrastructure’
RT: Germany seems to be focusing on offense as much as defense, when it comes to improving their cyber capabilities. Who and what do you think they want to attack?
Annie Machon: I think that is very interesting question: who do you want to attack with the cyberwarfare capabilities? Who precisely is the enemy these days? We know from the Snowden disclosures that Germany itself has been attacked aggressively by the NSA and GCHQ. We know from the Snowden disclosures that Germany itself has been aggressively targeting, attacking and intercepting the communications of its so-called European allies. So, whom precisely are they targeting now and why the army is getting involved as well as the [German foreign intelligence agency] BND [Bundesnachrichtendienst]?
RT: Defense is also highlighted as an important element in the new cyber plan for 2016. How much of this do you think is aimed at Germany’s own allies, the NSA, known now to spy on a host of politicians in Germany?
AM: I think the frontline of the battle these days now is not tanks, is not planes, it is cyberwarfare. Germany is certainly seems to be very willing to be complicit in working with the NSA to wage that war. I’m sure that it is pointing eastwards as well. It is a difficult one to try and predict…
RT: Do you think we’re coming to a time when conventional warfare operations will be used as a supplement to cyber wars, as opposed to the other way around?
AM: I think both will still have a role. However, I think most people underestimate the scope of what cyberwarfare can do. Infrastructure of all our countries is run over the internet now. It’s run by computers, be it electricity, be it the traffic signal control, be it train systems- wherever it is: banking, encryption – everything is dependent on cyber issues. So if you start waging cyberwarfare against the infrastructure of a nation state, then the whole nation state could collapse within a few days. If those basic levels of control, those basic levels of enablement for the society are taken away, then society will begin to collapse very quickly particularly in cities. I think this is very effective way of waging warfare if they chose to do it. The follow-up would then be with more conventional ways.
RT: Would you say Germany is developing with the times here, or are they behind the curve in terms of cyberwarfare, how do they measure up to say, the US?
AM:. … I’m sure they’ve been catching up for years. And that is partly where their dependence on the NSA technical capabilities has evolved from - they needed that to play catch up with the rest of the world. However I think they are very much in the field now. From what I’ve seen, the collusion with the NSA, they are very much part of the certain camp- to wage warfare against the rest of the world in the cyber realm.
RT: When it comes to conventional war – every government has an absolute advantage over regular people in terms of capability but it’s not necessarily the case in cyber space, as you need just a computer and the internet and knowledge of network protocols etc. Do you think we will see any hacker groups taking advantage of this and become more prominent players on the global stage?
AM: I think hacktivist groups are already taking a foot on the stage when it comes to this sort of warfare. We saw this only a couple of weeks ago with the story that German missiles placed in Turkey had been hacked, because they were US designed missiles with US designed software which of course is open to hacking, it has back doors. So this is going to come more, more prominent. And it is bit of sort of David and Goliath type asymmetrical information warfare. I think this is going to become more obvious, more prominent, not just with hacktivist groups but also with smaller countries which don’t necessarily have the military hardware to fight a conventional war. But they can’t push back against big countries with that hardware, and attack that software which runs their weapons. So it is asymmetric warfare, and I think it is going to become more predominant over the next decade or so.
Re: Indian Cyber Warfare Discussion
cyber security
What The Hack!
Our crucial computer systems are eminently breachable
Meetu Jain
What The Hack!
Our crucial computer systems are eminently breachable
Meetu Jain
Sceptics of the router leak suspect a determined ‘desi’ drive to hammer down Chinese manufacturers, but there is a clear economic rationale. The state-owned Mahanagar Telephone Nigam Limited (MTNL), for example, in its attempt to get the cheapest ADSL routers, chose to overlook a crucial security feature while awarding tenders to the lowest bidders. The routers were mainly bought from China as they are the cheapest at Rs 500 and did not have the crucial TR-69 interface, CERT officials say. The feature enables service providers to remotely plug or repair loopholes which would otherwise make these routers vulnerable. “Routers were not TR-69 compliant due to budget constraints.” Says advocate and cyber expert Prashant Mali, “When the leak was first discovered, the home ministry had recommended that we should stop buying routers and modems from companies like Huawei and zte. But countries like China objected and the issue got lost in red tape.”
Re: Indian Cyber Warfare Discussion
http://idrw.org/how-u-s-researchers-ide ... more-74433
Maybe not at the state dinner, but President Obama could put Chinese President Xi Jinping on the defensive with a simple question. “So, how’s Ge Xing these days?”
Ge Xing is an obscure officer in the People’s Liberation Army, operating in reconnaissance Unit 78020, out of the Chengdu Military Region. Only he’s not so obscure anymore. We know he’s behind a malware group known as Naikon. Using spear phishing emails with enticing Word documents, Naikon seeks to get secret information from users in the region of the South China Sea, including U.S. Navy and State Department information.
How do we know? Unit 78020 has been in the crosshairs of local cybersecurity companies ThreatConnect of Arlington and Defense Group Inc. of Vienna. They focused on Naikon for several years because it represented a nasty advance persistent threat (APT). They used the open-source Diamond Model for intrusion analysis.
You can read the findings here. But in essence, it’s another example of note just Chinese, but Chinese governmental cyber espionage. In other words, nothing to be shocked about, but a fine specimen nonetheless.
What I found interesting from my interview with Rich Barger, ThreatConnect’s chief intelligence officer, is that sharp Chinese officers can suffer from the same hubris as Western hackers who get slightly conceited and sloppy. The researchers were able to finger him by correlating his active and assertive social media activities. He used the online handle greensky, a domain name also associated with Naikon.
In fact, a Wall Street Journal account of Ge Xing shows some of the pictures he posted online. There’s greensky’s mountain bike for sale, together with an actual name and phone number. Here he’s visiting his family’s ancestral temple.
Barger says this politically knowledgeable officer simply made a common error that let researchers correlate a handle with the real person.
Speaking of the Naikon group, Barger said, “One of their operators [Ge] slipped up and was really able to give us some details as to who the actual entity was behind the keyboard — which is pretty rare in our industry.”
Re: Indian Cyber Warfare Discussion
Nearly 50 Pak websites hacked in reply to hacking of Kerala govt website
On Sunday, state woke up to the news that the official website of Kerala government - http://www.kerala.gov.in - was hacked allegedly by Pakistani hackers. The website had an image of burning Indian flag and messages such as Pakistan Zindabad", "We are Team Pak Cyber Attacker" and "Security is just an illusion". But a few expected a tit for tat reply and that it too within hours. An anonymous cyber group 'Mallu Cyber Soldiers' has hacked around 46 Pakistan websites, which include Pakistan's government website Pakistan.gov.pk, president.gov.pk and cabinet.gov.pk.
Re: Indian Cyber Warfare Discussion
Add this to our task of countering the PRC!
Intelligence agencies on board, Chinese tourists to get e-visas within 3 days
By Aman Sharma, ET Bureau | 26 Sep, 2015, 04.00AM IST
http://economictimes.indiatimes.com/art ... aign=cppst
Re: Indian Cyber Warfare Discussion
Massive cyber espionage racket run by Pakistan against Indian defence forces exposed
IBN Live: Go to the link and see the vedio
IBN Live: Go to the link and see the vedio
Re: Indian Cyber Warfare Discussion
Highly encrypted Cloud system of the army launched
A highly encrypted Cloud system of the Indian Army, similar to that of Google, which will store personnel as well operational data, was on Monday inaugurated by defence minister Manohar Parrikar in line with the force's plan to be a "digital army".
The 'Army Cloud' includes a central date centre, a near line data centre, both in Delhi and a disaster recovery site for a replication of its critical data along with virtualised servers and storage in an environmentally controlled complex.
This is an important step towards implementation of cyber security as it prelude to carrying of soft copies of data on CDs/DVDs and removable media, the officials said.
Re: Indian Cyber Warfare Discussion
Any mention of cloud makes me nervous. Airgaps should be maintained.
Re: Indian Cyber Warfare Discussion
Thakur sahab, it is private cloud  it seems to be running on defense network.
it seems to be running on defense network.
Re: Indian Cyber Warfare Discussion
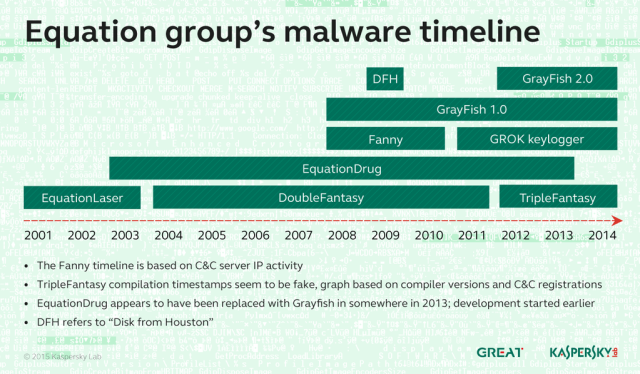
How “omnipotent” hackers tied to NSA hid for 14 years—and were found at last
"Equation Group" ran the most advanced hacking operation ever uncovered.
Equation Group's work
The LNK exploit as used by Fanny

An example of malicious PHP script Equation Group injected into hacked discussion forums
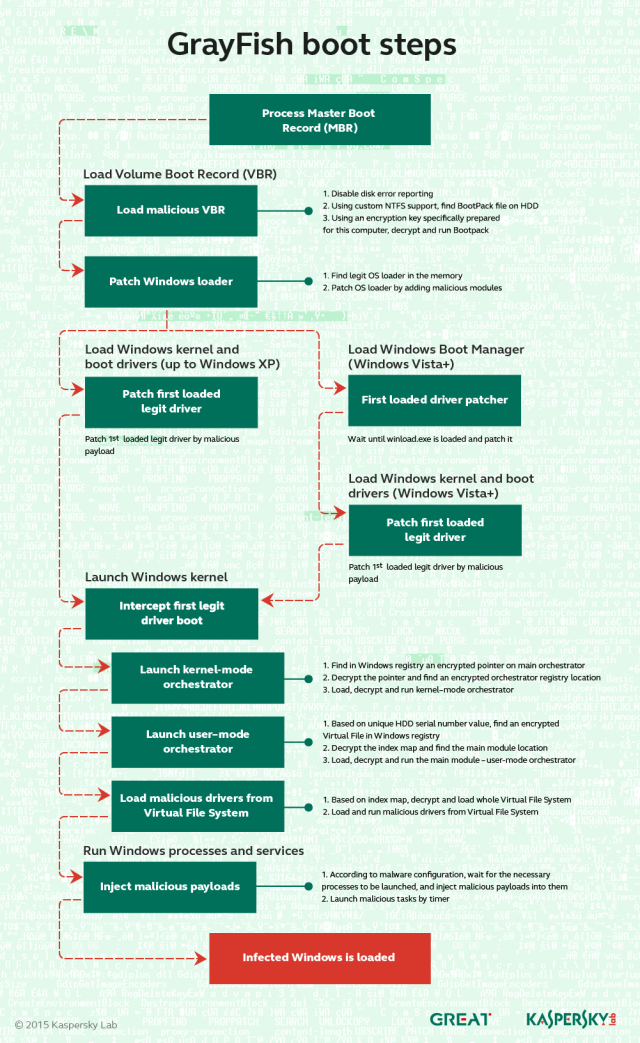
The VBR means Virtual Boot Record. It is a special area of the disk that is responsible for loading the operating system. The Pill is an injected piece of code ("blue pill", "red pill" - Matrix references) that is responsible for hijacking the OS loading. It works by carefully altering the loading mechanism to include malicious code that the OS blindly "swallows."
The BBSVC service is another GRAYFISH mechanism used when the Pill cannot be injected, for some unknown reason. It loads further stages of Grayfish at the time the OS starts. In essence, it's a weaker mechanism than the pill, because it exposes one single malicious executable on the hard drive of the victims. This is why BBSVC is a polymorphic executable, filled with gibberish and random data to make it hard to detect. The platform kernel "fvexpy.sys" is one of the core components of Grayfish. It is designed to run in Windows kernel mode and provide functions for the platform components

Mistakes were made
"Equation Group" ran the most advanced hacking operation ever uncovered.
CANCUN, Mexico — In 2009, one or more prestigious researchers received a CD by mail that contained pictures and other materials from a recent scientific conference they attended in Houston. The scientists didn't know it then, but the disc also delivered a malicious payload developed by a highly advanced hacking operation that had been active since at least 2001. The CD, it seems, was tampered with on its way through the mail.
It wasn't the first time the operators—dubbed the "Equation Group" by researchers from Moscow-based Kaspersky Lab—had secretly intercepted a package in transit, booby-trapped its contents, and sent it to its intended destination. In 2002 or 2003, Equation Group members did something similar with an Oracle database installation CD in order to infect a different target with malware from the group's extensive library. (Kaspersky settled on the name Equation Group because of members' strong affinity for encryption algorithms, advanced obfuscation methods, and sophisticated techniques.)
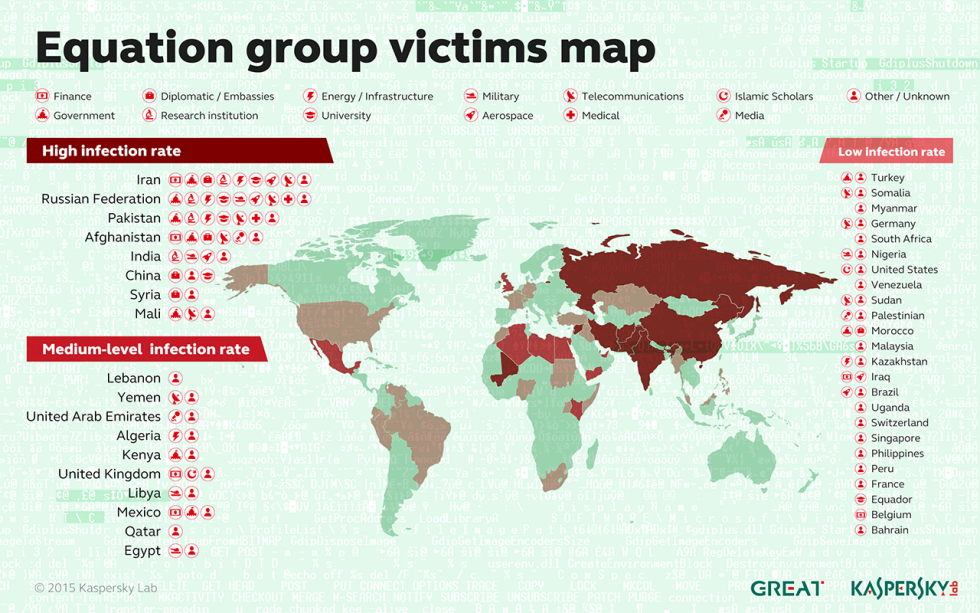
Kaspersky researchers have documented 500 infections by Equation Group in at least 42 countries, with Iran, Russia, Pakistan, Afghanistan, India, Syria, and Mali topping the list. Because of a self-destruct mechanism built into the malware, the researchers suspect that this is just a tiny percentage of the total; the actual number of victims likely reaches into the tens of thousands.
A long list of almost superhuman technical feats illustrate Equation Group's extraordinary skill, painstaking work, and unlimited resources. They include:
The use of virtual file systems, a feature also found in the highly sophisticated Regin malware. Recently published documents provided by Ed Snowden indicate that the NSA used Regin to infect the partly state-owned Belgian firm Belgacom.
The stashing of malicious files in multiple branches of an infected computer's registry. By encrypting all malicious files and storing them in multiple branches of a computer's Windows registry, the infection was impossible to detect using antivirus software.
Redirects that sent iPhone users to unique exploit Web pages. In addition, infected machines reporting to Equation Group command servers identified themselves as Macs, an indication that the group successfully compromised both iOS and OS X devices.
The use of more than 300 Internet domains and 100 servers to host a sprawling command and control infrastructure.
USB stick-based reconnaissance malware to map air-gapped networks, which are so sensitive that they aren't connected to the Internet. Both Stuxnet and the related Flame malware platform also had the ability to bridge airgaps.
An unusual if not truly novel way of bypassing code-signing restrictions in modern versions of Windows, which require that all third-party software interfacing with the operating system kernel be digitally signed by a recognized certificate authority. To circumvent this restriction, Equation Group malware exploited a known vulnerability in an already signed driver for CloneCD to achieve kernel-level code execution.
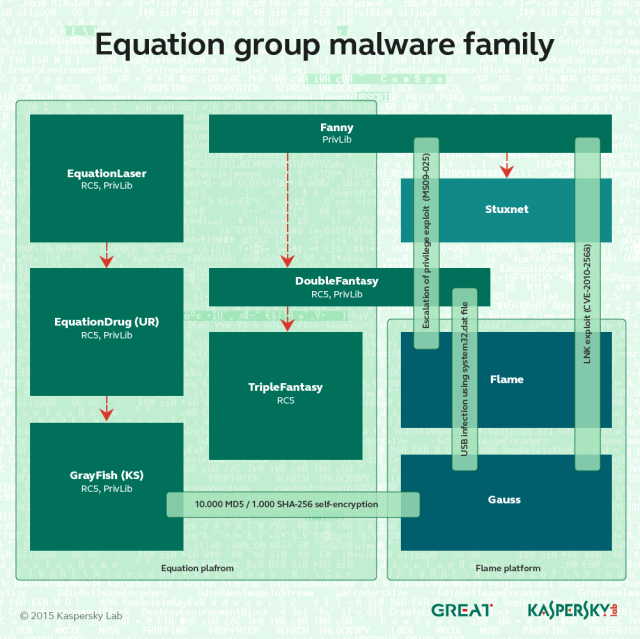
Taken together, the accomplishments led Kaspersky researchers to conclude that Equation Group is probably the most sophisticated computer attack group in the world, with technical skill and resources that rival the groups that developed Stuxnet and the Flame espionage malware.
"It seems to me Equation Group are the ones with the coolest toys," Costin Raiu, director of Kaspersky Lab's global research and analysis team, told Ars. "Every now and then they share them with the Stuxnet group and the Flame group, but they are originally available only to the Equation Group people. Equation Group are definitely the masters, and they are giving the others, maybe, bread crumbs. From time to time they are giving them some goodies to integrate into Stuxnet and Flame."
In an exhaustive report published Monday at the Kaspersky Security Analyst Summit here, researchers stopped short of saying Equation Group was the handiwork of the NSA—but they provided detailed evidence that strongly implicates the US spy agency.
First is the group's known aptitude for conducting interdictions, such as installing covert implant firmware in a Cisco Systems router as it moved through the mail.
Second, a highly advanced keylogger in the Equation Group library refers to itself as "Grok" in its source code. The reference seems eerily similar to a line published last March in an Intercept article headlined "How the NSA Plans to Infect 'Millions' of Computers with Malware." The article, which was based on Snowden-leaked documents, discussed an NSA-developed keylogger called Grok.
Third, other Equation Group source code makes reference to "STRAITACID" and "STRAITSHOOTER." The code words bear a striking resemblance to "STRAITBIZARRE," one of the most advanced malware platforms used by the NSA's Tailored Access Operations unit. Besides sharing the unconventional spelling "strait," Snowden-leaked documents note that STRAITBIZARRE could be turned into a disposable "shooter." In addition, the codename FOXACID belonged to the same NSA malware framework as the Grok keylogger.
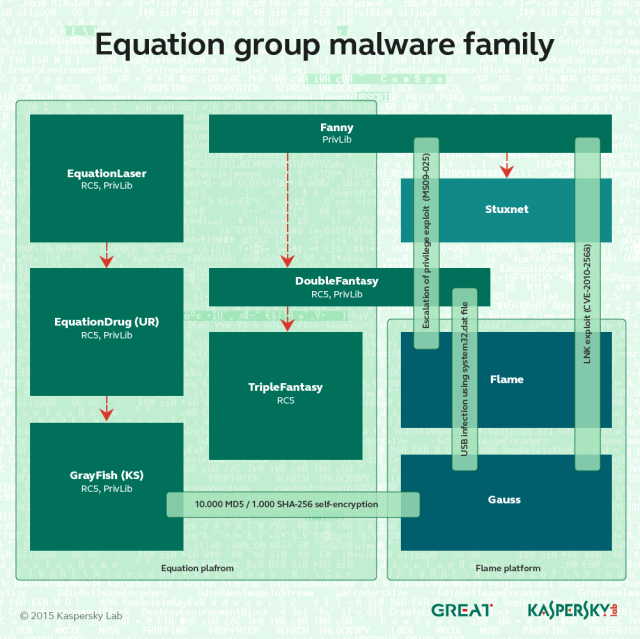
Apart from these shared code words, the Equation Group in 2008 used four zero-day vulnerabilities—including two that were later incorporated into Stuxnet.
The similarities don't stop there. Equation Group malware dubbed GrayFish encrypted its payload with a 1,000-iteration hash of the target machine's unique NTFS object ID. The technique makes it impossible for researchers to access the final payload without possessing the raw disk image for each individual infected machine. The technique closely resembles one used to conceal a potentially potent warhead in Gauss, a piece of highly advanced malware that shared strong technical similarities with both Stuxnet and Flame. (Stuxnet, according to The New York Times, was a joint operation between the NSA and Israel, while Flame, according to The Washington Post, was devised by the NSA, the CIA, and the Israeli military.)
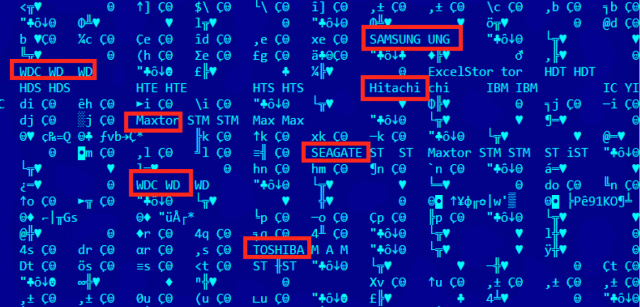
Beyond the technical similarities to the Stuxnet and Flame developers, Equation Group boasted the type of extraordinary engineering skill people have come to expect from a spy organization sponsored by the world's wealthiest nation. One of the Equation Group's malware platforms, for instance, rewrote the hard-drive firmware of infected computers—a never-before-seen engineering marvel that worked on 12 drive categories from manufacturers including Western Digital, Maxtor, Samsung, IBM, Micron, Toshiba, and Seagate.
The malicious firmware created a secret storage vault that survived military-grade disk wiping and reformatting, making sensitive data stolen from victims available even after reformatting the drive and reinstalling the operating system. The firmware also provided programming interfaces that other code in Equation Group's sprawling malware library could access. Once a hard drive was compromised, the infection was impossible to detect or remove.
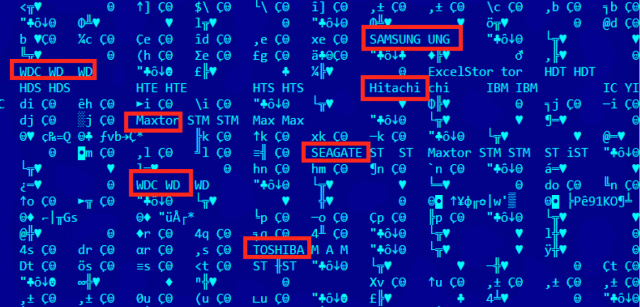
Forensics software displays some of the hard drives Equation Group was able to commandeer using malicious firmware.
While it's simple for end users to re-flash their hard drives using executable files provided by manufacturers, it's just about impossible for an outsider to reverse engineer a hard drive, read the existing firmware, and create malicious versions.
"This is an incredibly complicated thing that was achieved by these guys, and they didn't do it for one kind of hard drive brand," Raiu said. "It's very dangerous and bad because once a hard drive gets infected with this malicious payload it's impossible for anyone, especially an antivirus [provider], to scan inside that hard drive firmware. It's simply not possible to do that."
Equation Group's work
One of the most intriguing elements of Equation Group is its suspected use of interdiction to infect targets. Besides speaking to the group's organization and advanced capabilities, such interceptions demonstrate the lengths to which the group will go to infect people of interest. The CD from the 2009 Houston conference—which Kaspersky declined to identify, except to say it was related to science—tried to use the autorun.inf mechanism in Windows to install malware dubbed DoubleFantasy. Kaspersky knows that conference organizers did send attendees a disc, and the company knows the identity of at least one conference participant who received a maliciously modified one, but company researchers provided few other details and don't know precisely how the malicious content wound up on the disc.
"It would be very easy to trace the attack back to the organizers and point them out, and this could in turn result in some very serious diplomatic incidents," Raiu said. "Our best guess is that the organizers didn't act in a malicious way against the participants, but [that] some of the CD-ROMs on their way to the participants were intercepted and replaced with the malicious variants."
Even less is known about a CD for installing Oracle 8i-8.1.7 for Windows sent six or seven years earlier, except that it installed an early Equation Group malware program known as EquationLaser. The conference and Oracle CDs are the only Equation Group interdictions that Kaspersky researchers have discovered. Given how little is known about the interdictions, they weren't likely to have been used often.
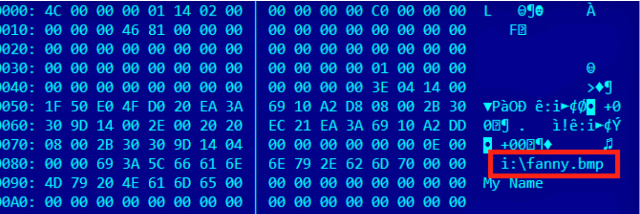
A separate method of infection relied on a worm introduced in 2008 that Kaspersky has dubbed Fanny, after a text string that appears in one of the zero-day exploits used by the worm to self-replicate. The then-unknown vulnerability resided in functions that process so-called .LNK files Windows uses to display icons when a USB stick is connected to a PC. By embedding malicious code inside the .LNK files, a booby-trapped stick could automatically infect the connected computer even when its autorun feature was turned off. The self-replication and lack of any dependence on a network connection made the vulnerability ideal for infecting air-gapped machines. (The .LNK vulnerability is classified as CVE-2010-2568.)
Some two years after first playing its role in Fanny, the .LNK exploit was added to a version of Stuxnet so that the worm could automatically spread through highly sensitive computers in Iran. Fanny also relied on an elevation-of-privilege vulnerability that was a zero day at the time the worm was introduced. In 2009, the exploit also made its way into Stuxnet, but by then, Microsoft had patched the underlying bug with the release of MS09-025.
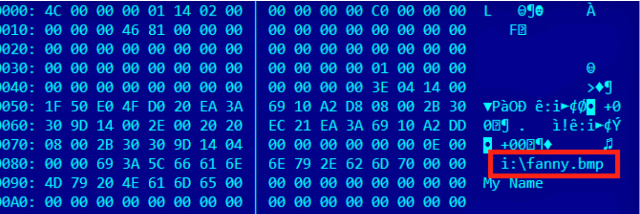
The LNK exploit as used by Fanny
A far more common infection vector was Web-based attacks that exploited vulnerabilities in Oracle's Java software framework or in Internet Explorer. The exploits were hosted on a variety of websites related to everything from reviews of technology products to discussions of Islamic Jihad. In addition to planting exploits on the websites, the attack code was also transmitted through ad networks. The wide range of exploit carriers may explain why so many of the machines Kaspersky observed reporting to its sinkholes were domain controllers, data warehouses, website hosts, and other types of servers. Equation Group, it seems, wasn't infecting only end user computers—it was also booby-trapping servers known to be accessed by targeted end users.
Equation Group exploits are notable for the surgical precision exercised to ensure that only an intended target was infected. One Equation Group-written PHP script that Kaspersky unearthed, for instance, checked if the MD5 hash of a website visitor's username was either 84b8026b3f5e6dcfb29e82e0b0b0f386 or e6d290a03b70cfa5d4451da444bdea39. The plaintext corresponding to the first hash is "unregistered," an indication that attackers didn't want to infect visitors who weren't logged in. The second hash has yet to be deciphered Update: now been cracked; see this brief.
"We could not crack this MD5, despite using considerable power for several weeks, which makes us believe [the plaintext username] is a relatively complex one," Raiu said. "It definitely indicates that whoever is behind this username should not be infected by the Equation Group, [and] actually it shouldn't even see the exploit. I would assume this is either one of the group members (a fake identity), one of their partners, or a known identity of a previously infected victim."
The PHP script also took special care not to infect IP addresses based in Jordan, Turkey, and Egypt. Kaspersky observed users visiting the site who didn't meet any of these exceptions, yet they still weren't attacked—an indication that an additional level of filtering spared all but the most sought-after targets who visited the site.

An example of malicious PHP script Equation Group injected into hacked discussion forums
More recently, Kaspersky has observed malicious links on the site standardsandpraiserepurpose[.]com that looked like
standardsandpraiserepurpose[.]com/login?qq=5eaae4d[SNIP]0563&rr=1&h=cc593a6bfd8e1e26c2734173f0ef75be3527a205
Six codenameswhere the h value (that is, the text following the "h=") appears to be an SHA1 hash. Kaspersky has yet to crack those hashes, but company researchers suspect they're being used to serve customized exploits to specific people. The company is recruiting help from fellow white-hat hackers in cracking them. Other hashes include:
0044c9bfeaac9a51e77b921e3295dcd91ce3956a
06cf1af1d018cf4b0b3e6cfffca3fbb8c4cd362e
3ef06b6fac44a2a3cbf4b8a557495f36c72c4aa6
5b1efb3dbf50e0460bc3d2ea74ed2bebf768f4f7
930d7ed2bdce9b513ebecd3a38041b709f5c2990
e9537a36a035b08121539fd5d5dcda9fb6336423
The PHP exploit code also serves unique Web pages and HTML code to people visiting with iPhones, behavior that Kaspersky found telling.
"This indicates the exploit server is probably aware of iPhone visitors and can deliver exploits for them as well," Kaspersky's report published Monday explained. "Otherwise, the exploitation URL can simply be removed for these." The report also said one sinkholed server receives visits from a large pool of China-based machines that identify themselves as Macs in the browser user agent string. While Kaspersky has yet to obtain Equation Group malware that runs on OS X, they believe it exists.
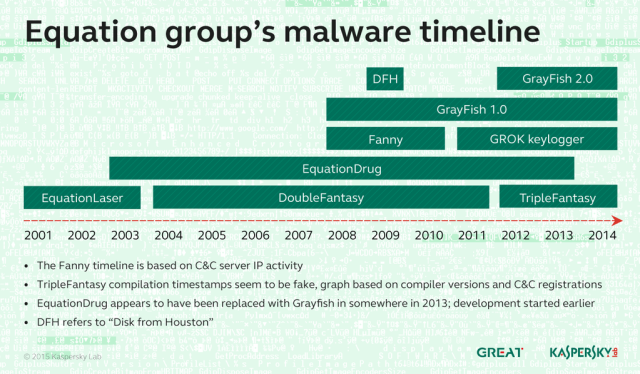
In all, Kaspersky has tied at least six distinct pieces of malware to Equation Group. They include:
EquationLaser: an early implant in use from 2001 to 2004.
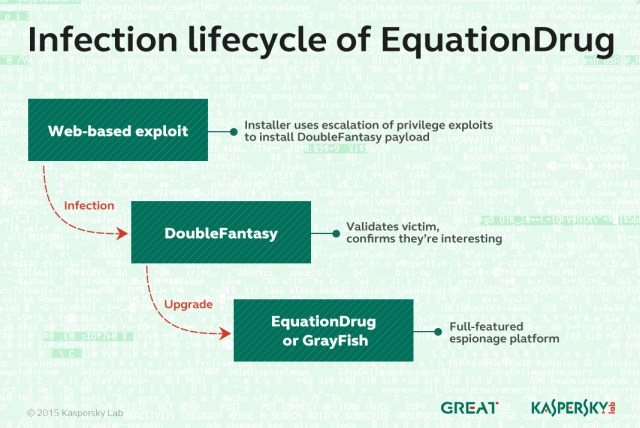
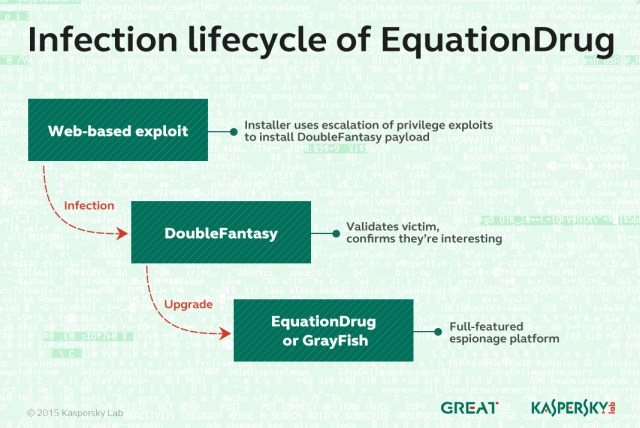
DoubleFantasy: a validator-style trojan designed to confirm if the infected person is an intended target. People who are confirmed get upgraded to either EquationDrug or GrayFish.
EquationDrug: also known as Equestre, this is a complex attack platform that supports 35 different modules and 18 drivers. It is one of two Equation Group malware platforms to re-flash hard drive firmware and use virtual file systems to conceal malicious files and stolen data.
It was delivered only after a target had been infected with DoubleFantasy and confirmed to be a target. It was introduced in 2002 and was phased out in 2013 in favor of the more advanced GrayFish.
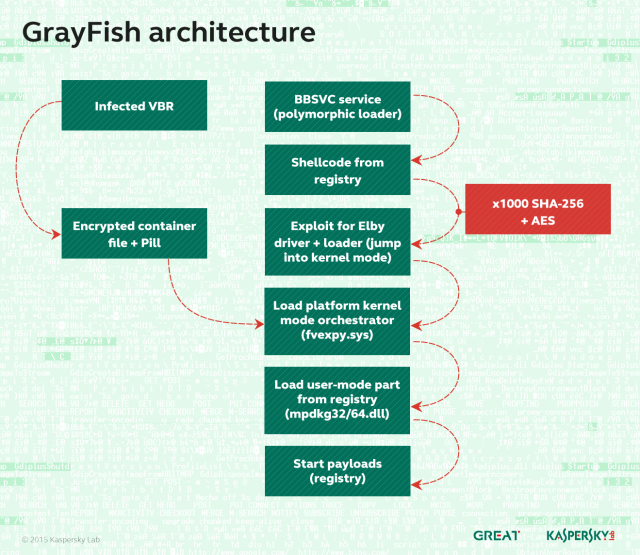
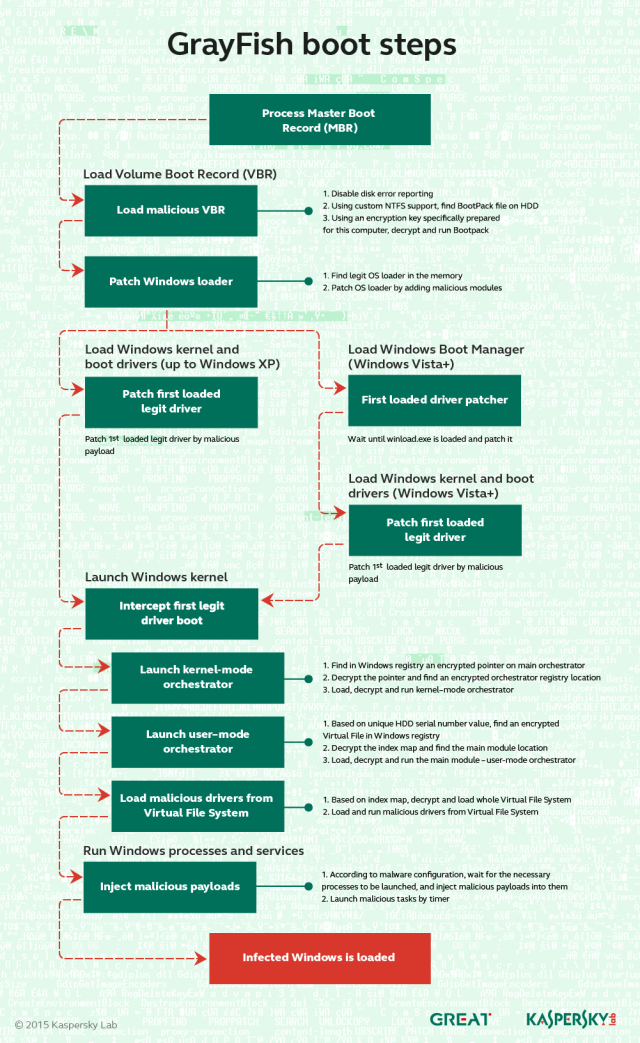
Grayfish: the successor to EquationDrug and the most sophisticated of all the Equation Group attack platforms. It resides completely in the registry and relies on a bootkit to take hold each time a computer starts. Whereas EquationDrug re-flashed hard drives for six models, GrayFish re-flashed 12 classes of hard drives. GrayFish exploits a vulnerability in the CloneCD driver ElbyCDIO.sys—and possibly drivers of other programs—to bypass Windows code-signing requirements.
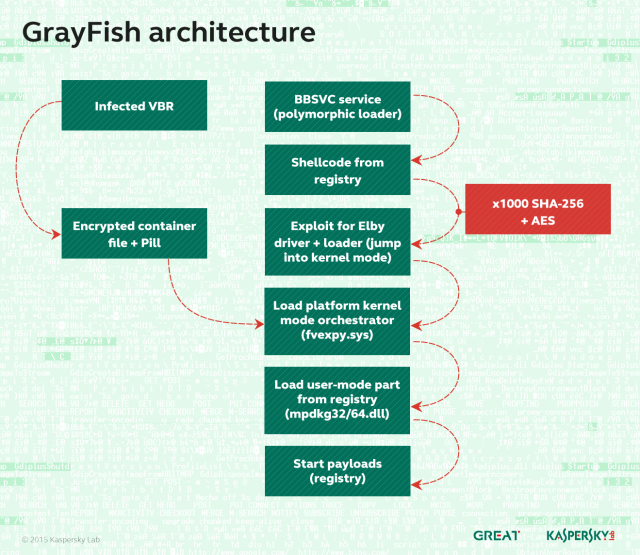
The VBR means Virtual Boot Record. It is a special area of the disk that is responsible for loading the operating system. The Pill is an injected piece of code ("blue pill", "red pill" - Matrix references) that is responsible for hijacking the OS loading. It works by carefully altering the loading mechanism to include malicious code that the OS blindly "swallows."
The BBSVC service is another GRAYFISH mechanism used when the Pill cannot be injected, for some unknown reason. It loads further stages of Grayfish at the time the OS starts. In essence, it's a weaker mechanism than the pill, because it exposes one single malicious executable on the hard drive of the victims. This is why BBSVC is a polymorphic executable, filled with gibberish and random data to make it hard to detect. The platform kernel "fvexpy.sys" is one of the core components of Grayfish. It is designed to run in Windows kernel mode and provide functions for the platform components
GrayFish is the crowning achievement of the Equation Group. The malware platform is so complex that Kaspersky researchers still understand only a fraction of its capabilities and inner workings. Key to the sophistication of GrayFish is its bootkit, which allows it to take extraordinarily granular control of the machines it infects.
"This allows it to control the launching of Windows at each stage," Kaspersky's written report explained. "In fact, after infection, the computer is not run by itself anymore: it is GrayFish that runs it step by step, making the necessary changes on the fly."
Fanny: A computer worm that exploited what in 2008 were two zero-day vulnerabilities in Windows to self-replicate each time an infected USB stick was inserted into a targeted computer. The main purpose of Fanny was to conduct reconnaissance on sensitive air-gapped networks. After infecting a computer not connected to the Internet, Fanny collected network information and saved it to a hidden area of the USB drive. If the stick was later plugged in to an Internet-computer, it would upload the data to attacker servers and download any attacker commands. If the stick was later plugged into the air-gapped machine, the downloaded commands would be executed. This process would continue each time the stick was switched between air-gapped and Internet-connected machines.

TripleFantasy: A full-featured backdoor sometimes used in tandem with GrayFish.
Mistakes were made
Hacking without a budgetNo matter how elite a hacking group may be, Raiu said, mistakes are inevitable. Equation Group made several errors that allowed Kaspersky researchers to glean key insights into an operation that went unreported for at least 14 years.
Kaspersky first came upon the Equation Group in March 2014, while researching the Regin software that infected Belgacom and a variety of other targets. In the process, company researchers analyzed a computer located in the Middle East and dubbed the machine "Magnet of Threats" because, in addition to Regin, it was infected by four other highly advanced pieces of malware, including Turla, Careto/Mask, ItaDuke, and Animal Farm. A never-before-seen sample of malware on the computer piqued researchers' interest and turned out to be an EquationDrug module.
Following the discovery, Kaspersky researchers combed through their cloud-based Kaspersky Security Network of exploits and infections reported by AV users and looked for similarities and connections. In the following months, the researchers uncovered additional pieces of malware used by Equation Group as well as the domain names used to host command channels.
Perhaps most costly to the attackers was their failure to renew some of the domains used by these servers. Out of the 300 or so domains used, about 20 were allowed to expire. Kaspersky quickly registered the domains and, over the past ten months, has used them to "sinkhole" the command channels, a process in which researchers monitor incoming connections from Equation Group-infected machines.
One of the most severe renewal failures involved a channel that controlled computers infected by "EquationLaser," an early malware platform abandoned around 2003 when antivirus programs began to detect it. The underlying domain name remained active for years until one day, it didn't; Kaspersky acquired it and EquationLaser-infected machines still report to it.
"It's really surprising to see there are victims around the world infected with this malware from 12 years ago," Raiu said. He continues to see about a dozen infected machines that report from countries that include Russia, Iran, China, and India.
Raiu said 90 percent or more of the command and control servers were closed last year, although some remained active as recently as last month.
"We understand just how little we know. It also makes us reflect about how many other things remain hidden or unknown."
The sinkholes have allowed Kaspersky researchers to gather key clues about the operation, including the number of infected computers reporting to the seized command domains, the countries in which these compromised computers are likely located, and the types of operating systems they run.
Another key piece of information gleaned by Kaspersky: some machines infected by Equation Group are the "patients zero" that were used to seed the Stuxnet worm so it would travel downstream and infect Iran's Natanz facility .
"It is quite possible that the Equation Group malware was used to deliver the Stuxnet payload," Kaspersky researchers wrote in their report.
Other key mistakes were variable names, developer account names, and similar artifacts left in various pieces of Equation Group malware. In the same way cat burglars wear gloves to conceal their fingerprints, attackers take great care to scrub such artifacts out of their code before releasing it. But in at least 13 cases, they failed. Possibly the most telling artifact is the string "-standalonegrok_2.1.1.1" that accompanies a highly advanced keylogger tied to Equation Group.
Another potentially damaging artifact found by Kaspersky is the Windows directory path of "c:\users\rmgree5" belonging to one of the developer accounts that compiled Equation Group malware. Assuming the rmgree5 wasn't a randomly generated account name, it may be possible to link it to a developer's real-world identity if the handle has been used for other accounts or if it corresponds to a developer's real-world name such as "Richard Gree" or "Robert Greenberg."
Kaspersky researchers still don't know what to make of the 11 remaining artifacts, but they hope fellow researchers can connect the strings to other known actors or incidents. The remaining artifacts are:
SKYHOOKCHOW
prkMtx - unique mutex used by the Equation Group's exploitation library (gPrivLibh)
"SF" - as in "SFInstall", "SFConfig"
"UR", "URInstall" - "Performing UR-specific post-install..."
"implant" - from "Timeout waiting for the "canInstallNow" event from the implant-specific EXE!"
STEALTHFIGHTER (VTT/82055898/STEALTHFIGHTER/2008-10-16/14:59:06.229-04:00
DRINKPARSLEY - (Manual/DRINKPARSLEY/2008-09-30/10:06:46.468-04:00)
STRAITACID - (VTT/82053737/STRAITACID/2008-09-03/10:44:56.361-04:00)
LUTEUSOBSTOS - (VTT/82051410/LUTEUSOBSTOS/2008-07-30/17:27:23.715-04:00)
STRAITSHOOTER - STRAITSHOOTER30.exe
DESERTWINTER - c:\desert~2\desert~3\objfre_w2K_x86\i386\DesertWinterDriver.pdb
The money and time required to develop the Equation Group malware, the technological breakthroughs the operation accomplished, and the interdictions performed against targets leave little doubt that the operation was sponsored by a nation-state with nearly unlimited resources to dedicate to the project. The countries that were and weren't targeted, the ties to Stuxnet and Flame, and the Grok artifact found inside the Equation Group keylogger strongly support the theory the NSA or a related US agency is the responsible party, but so far Kaspersky has declined to name a culprit.
Update: Reuters reporter Joseph Menn said the hard-drive firmware capability has been confirmed by two former government employees. He wrote:
A former NSA employee told Reuters that Kaspersky's analysis was correct, and that people still in the intelligence agency valued these spying programs as highly as Stuxnet. Another former intelligence operative confirmed that the NSA had developed the prized technique of concealing spyware in hard drives, but said he did not know which spy efforts relied on it.
Update: Several hours ater this post went live, NSA officials e-mailed the following statement to Ars:
We are aware of the recently released report. We are not going to comment publicly on any allegations that the report raises, or discuss any details. On January 17, 2014, the President gave a detailed address about our signals intelligence activities, and he also issued Presidential Policy Directive 28 (PPD-28). As we have affirmed publicly many times, we continue to abide by the commitments made in the President’s speech and PPD-28. The U.S. Government calls on our intelligence agencies to protect the United States, its citizens, and its allies from a wide array of serious threats - including terrorist plots from al-Qaeda, ISIL, and others; the proliferation of weapons of mass destruction; foreign aggression against ourselves and our allies; and international criminal organizations.
What is safe to say is that the unearthing of the Equation Group is a seminal finding in the fields of computer and national security, as important, or possibly more so, than the revelations about Stuxnet.
"The discovery of the Equation Group is significant because this omnipotent cyber espionage entity managed to stay under the radar for almost 15 years, if not more," Raiu said. "Their incredible skills and high tech abilities, such as infecting hard drive firmware on a dozen different brands, are unique across all the actors we have seen and second to none. As we discover more and more advanced threat actors, we understand just how little we know. It also makes us reflect about how many other things remain hidden or unknown."
Re: Indian Cyber Warfare Discussion
The Shadow Brokers: Has Someone Hacked The NSA?
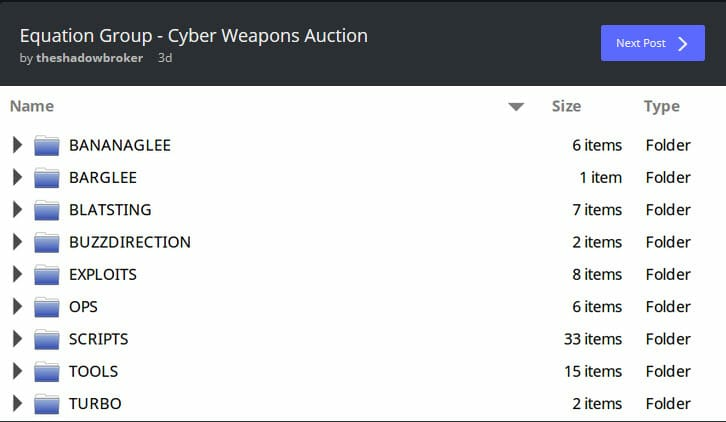
Unlikely HackHackers calling themselves ‘The Shadow Brokers’ have penetrated NSA government spies, making off with important surveillance tools in the process. The unknown hackers have declared that they intend to sell off those cyber exploits in a forthcoming auction, presumably on the dark web.
The surveillance tools have reportedly been stolen from the servers of a hacking collective known as ‘Equation Group‘. That group is thought to be the most elite branch of NSA hackers. Among the software taken is malware, hacking tools (akin to those taken from Hacking Team last year), and private exploits used during NSA surveillance operations.
As unlikely as the hack seems, most cybersecurity experts agree that the cyber attack looks legitimate. Whoever the hackers are, they seem to have taken what they claim.
The Million Bitcoin Exploit Sell-offAlthough little is actually known about ‘Equation Group,’ a report released last year by Russian cyber security firm Kaspersky said that the surveillance operation was,
‘A threat actor that surpasses anything known in terms of complexity and sophistication of techniques, and that has been active for almost two decades.’
With that in mind, it would appear that whoever ‘The Shadow Brokers’ are, they have taken one of the most active and powerful surveillance teams on earth by storm. In a surprise offensive that has got tongues wagging throughout the cyber security industry.
In addition to the preliminary data-dump (that has so far served to corroborate the cunning hackers’ claims), the Shadow Brokers are threatening to sell the contents of the cyber penetration in an online auction. Those cybercriminals claim that they plan to auction-off the stolen hacking tools for a whopping 1 Million Bitcoins (about $568 Million).
Equation Group and the NSAAccording to the hackers (who wrote in imperfect English on a number of blogs – including Tumblr), the hacking tools they plan to sell for that lofty sum will allow the winning bidder to penetrate prominent industry firewalls by firms such as Cisco Systems Inc, Juniper Networks Inc, Fortinet Inc and TopSec.
As of yet, those companies (and the NSA) have failed to pass comment on the hackers’ claims. One would imagine, however, that behind closed doors the NSA are running around like headless chickens at the thought of their elite hacking team’s secrets being sold off online.
Who are the Shadow Brokers?In its report from 2015, Moscow-based security firm Kaspersky commented that it had found evidence that Equation Group had infected a huge number of personal computers with its private exploits. Earlier this year, Kaspersky released new revelations detailing that the NSA’s surveillance team had discovered a way to hide exploits within the hard drives of top technology firms including Seagate, Western Digital, and Toshiba. According to those reports, that means that the NSA-linked hackers have the capability to spy on huge numbers of computers around the world.
On top of that, Kaspersky claimed it had found evidence of the NSA’s tools within computers from 30 countries. Among those, the most infected places where Iran, Russia, Pakistan, Afghanistan, China, Mali, Syria, Yemen, and Algeria. Locations which add credence to the allegations that it was cyber warfare executed at the hands of the NSA.
Within the published data (relating to places found to be infected by Equation Group) stark evidence was found of ‘medium infection rates’ within the UK. Revealing that even US allies were subjected to infections at the hands of the NSA’s spies. Hardly surprising, considering the levels of domestic surveillance that were shown to be occurring by the Snowden revelations.
On a side note, Equation Group has also been linked to the famous Regin and Stuxnet attacks. Attacks which are believed to have been US-led initiatives, and include the Stuxnet attack on Iran’s Natanz nuclear power station back in 2013.
Most Wanted!So far, online posts from the mysterious Shadow Brokers have been posted to Tumblr, Pastebin and GitHub. In those posts, the following message was found,
‘How much you pay for enemies cyber weapons? Not malware you find in networks. Both sides, RAT + LP, full state sponsor tool set? We find cyber weapons made by creators of Stuxnet, duqu, flame. Kaspersky calls Equation Group. We follow Equation Group traffic. We find Equation Group source range. We hack Equation Group. We find many many Equation Group cyber weapons. You see pictures. We give you some Equation Group files free, you see. This is good proof no? You enjoy!!! You break many things. You find many intrusions. You write many words. But not all, we are auction the best files.’
Does Snowden know something!?The comment appears to reveal the hackers’ wish to sell the contents of the cyber attack onto enemies of the US. A rather frank admission that could see whoever carried out the incredibly ostentatious act of hacking placed high on the US’ most wanted list.
After all, consider the infamous hacker Guccifer (Marcel Lazăr Lehel from Romania; not to be confused with Guccifer 2.0), who hacked a number of high profile US targets and found himself extradited to the US to face charges. With that in mind, it seems obvious that whoever has dared to penetrate what is considered to be the number 1 spy agency in the world, will likely be a highly wanted person in the US should the hackers’ real identities ever be uncovered.
So far not much is known about the hackers. What is known, however, is that the Shadow Brokers appear to have been preparing for this release since the beginning of August. At that time, their Reddit, Twitter, Imgur, and Github accounts were all suddenly created. In preparation for their – currently circulating – message, which unlike most data dumps seems to be some kind of advertising campaign for the forthcoming auction of Equation Group’s cyber exploits.
Suspicious Timing?Edward Snowden has also gone on the record today with his belief that the hackers may be acting from within Russia. That theory, he claims, is due to the fact that many of the files that have been dumped so far are dated from 2013. Snowden says he finds that (and the timing of the data dump’s proximity to the ongoing DNC debacle) suspicious. What the dates do demonstrate, is that whoever the Shadow Brokers are, they have been sitting on this data for three years.
‘Circumstantial evidence and conventional wisdom indicates Russian responsibility,’ Snowden commented on Twitter. Followed by, ‘this leak is likely a warning that someone can prove US responsibility for any attacks that originated from this malware server.’
What is a little perplexing, is that no one appears to be able to confirm what Snowden considers this ‘circumstantial evidence’ to be. A point that – despite being asked – he has not come forward to clear up. Leading myself (and other cyber security analysts) to ponder on the meaning of his words.
Is Snowden’s implying some sort of inside information about the Shadow Brokers? And if that is the case; what does Snowden know!?
One thing is for certain. With the timing of the events surrounding the Shadow Brokers and Snowden’s cryptic Tweets from earlier this month, one can’t help wondering if Snowden is somehow involved.
On Friday the 5th of August, Snowden suddenly Tweeted a 64 character code that was then rapidly deleted. Hours before that key code was released, the infamous privacy-hero Tweeted the rather cryptic message ‘It’s Time’. In a message apparently directed at his former NSA colleagues.
With this NSA-related hack suddenly hitting the news – and Snowden’s hints that he may know more than he is letting on – one can’t help pondering if this is what it was time for. For now, however, I admit that those thoughts are wild conjecture.
Re: Indian Cyber Warfare Discussion
The shadow brokers could very well be Russians. They are capable of this, have the necessary resources and the intent.
The list of countries given there - Iran, Russia, Pakistan, Afghanistan, China, Mali, Syria, Yemen, and Algeria. Apart from may be Mali and Russia itself, Russians have a huge need to what is happening all those countries. Strange that India is not on that list, assuming you can take it as truth.
The list of countries given there - Iran, Russia, Pakistan, Afghanistan, China, Mali, Syria, Yemen, and Algeria. Apart from may be Mali and Russia itself, Russians have a huge need to what is happening all those countries. Strange that India is not on that list, assuming you can take it as truth.
Re: Indian Cyber Warfare Discussion
Cross post from the STFUP thread
g.sarkar wrote:g.sarkar wrote: http://www.sify.com/news/indian-techies ... cfgej.html
Indian techies hit back, lock Pakistan govt computers
New Delhi: Indian hackers have carried out a massive cyber attack on Pakistani government network and claim to have locked their computers and data using 'Ransomeware' Act against Hafiz Sayeed voice grow louder in Pakistan The Indian attack came after various Indian websites faced attack by Pakistani hackers few days ago. On 3 October, the National Green Tribunal's (NGT) website came under attack with a group hacking it and posting objectionable comments, claiming it was an act of 'revenge' against the Indian Army's surgical strikes across the Line of Control. "Website stamped by D4RK 4NG31," read the title message on the homepage of the NGT's site. The website was left with a page filled with curse words and the Pakistani national anthem as a background track. "We are Unbeatable. You m*** kill innocent people in Kashmir and call yourself defenders of your country. You *** violate the ceasefire on border and call it 'Surgical Strikes'. Now kiss the **** of Cyber War," the Pakistani had hackers said. To counter the offensive, Indian hackers have now locked Pakistan government computers. Cyber crime experts in India claim that 'anonymous' hacker have infected Pakistan government systems and have taken control over hundreds of computers, making them inaccessible.
......
Gautam
Re: Indian Cyber Warfare Discussion
Not sure if this was posted earlier.
Indian hacking gang goes on three-year Chinese phishing trip
Extract: Suspected hackers based in India have compromised thousands of computers, going about their business as far back as 2013.
::
"The overarching campaign appears to target both Chinese nationals within different industries and government agencies in Southern Asia," the research trio say.
Indian hacking gang goes on three-year Chinese phishing trip
Extract: Suspected hackers based in India have compromised thousands of computers, going about their business as far back as 2013.
::
"The overarching campaign appears to target both Chinese nationals within different industries and government agencies in Southern Asia," the research trio say.
Re: Indian Cyber Warfare Discussion
Revenge for Assange ?
U.S. internet disrupted as firm hit by cyberattacks
U.S. internet disrupted as firm hit by cyberattacks
List of sites affectedTwitter experienced renewed outages Friday afternoon following hours of internet disruption that took down numerous sites earlier in the morning across the U.S. East Coast.
A wave of reports of problems accessing many popular websites came after the servers at a major internet management firm were hit by several cyberattack.
New Hampshire-based Dyn said its server infrastructure suffered a distributed denial-of-service (DDoS) attack, which occurs when a system is overwhelmed by malicious electronic traffic.
“It doesn’t look like a kid in a basement with a laptop,” said CBS News’ homeland security correspondent Frances Townsend. “It looks more sophisticated.”
A second attack around noon affected even the FBI, CBS News’ Chip Reid reported.
Re: Indian Cyber Warfare Discussion
There are claims that China has nearly 1.2 lac registered cyber security experts in contrast to India which has around 600. One chinese expert boasted that it would take China around 6 hours to overwhelm the relatively primitive Indian cyber infra such as banking, communications and power grids. Particularly since China has invested quite a lot offensive and defensive cyber weaponry, particularly investment in massive supercomputers and software. The present hack of bank visa/MasterCard/Rupay credit/debit cards to be thought in this context.
Re: Indian Cyber Warfare Discussion
this news regarding the compromising of debit cards due to self deleting malware installed
http://economictimes.indiatimes.com/ind ... 987336.cms
excerpts
http://economictimes.indiatimes.com/ind ... 987336.cms
excerpts
CERT-In had instructed banks on October 7 to stay alert in wake of surgical strikes India's Computer Emergency Response Team (CERT-In), the government's apex watchdog against cyberattacks, had instructed banks to be on heightened alert as recently as two weeks ago even as a malware infection was spreading through their networks and spawning the country's biggest known breach of financial data. The agency, which frequently sends advisories to banks and other financial institutions about possible threats to their systems, had also sent warnings in July and August, a t ..August, a top government official told ET.
The latest of these on October 7 warned about 'expected targeted attacks from Pakistan", in the wake of India's counterstrike across the border following terrorist attacks in Jammu and Kashmir. At the time this advisory was sent, more than a month had elapsed since the first complaints stemming from the breach began streaming into banks in early September. The malware infection put 3.2 million debit cards at risk, although the loss — through unauthorised withdrawals across the world — has been pegged at a relatively minor Rs 1.3 crore by the National Payments Corporation of India (NPCI). The government and the Reserve Bank of India have ordered banks and payment gateways to investigate the breach amid concerns that faster, concerted action could have limited the extent of the attack.
Re: Indian Cyber Warfare Discussion
Powerful Greek Army Hacker Breaches High Commission Websites in India
India is making the security headlines once again, this time after hackers managed to break into some of the high commission websites in the country and access login information of hundreds of users.
Kapustkiy, who describes himself as a security pentester and who is now a member of the Powerful Greek Army, accessed the database of two different high commission websites in India using an SQL injection that eventually exposed credentials of nearly 200 accounts, as he told us.
The High Commission of Ghana and the High Commission of Finland, both from India, were breached a few hours ago by Kapustkiy, who also decided to leak part of the database in order to give IT admins the time they need to patch the vulnerabilities.
Authorities ignoring security reports
Oddly enough, Kapustkiy says that he decided to breach Indian websites after local authorities failed to boost security and address the vulnerabilities that he previously discovered and which he used to access credentials of thousands of users.
“I had spoken with Yatin Patel (he runs all those sites) and he promised me a while ago that he would take a seriously look to it,” he told us earlier today. “I kept sending him emails but I did not get anything back from them because they claimed that they have fixed everything which is not true.”
What’s even more awkward is that Indian authorities publicly acknowledged vulnerabilities discovered by Kapustkiy and issued a thank you statement for the security pentester to show their appreciation for helping them address flaws that could expose users.
“Thank you for your advice,” Sanjay Kumar Verma, Joint Secretary, eGovernance and Information Technology, said recently. “We are fixing codes one by one. Your help in probing websites of various Indian embassies is a great help.”
Indian security engineers are more likely to look into this latest breach now that it went public, but in the future, it might be a good idea to actually fix them before user information is exposed.
Re: Indian Cyber Warfare Discussion
INDIA TO USE INDIGENOUS OPERATING SYSTEM TO ENHANCE CYBER SECURITY
In line with Prime Minister Narendra Modi's push for enhancing cyber security, the Indian Army is testing the indigenous BOSS, (Bharat Operating System Solutions) to guard its communication and information networks from espionage by foreign players.
In his maiden address to the senior commanders of the three services, the prime minister had asked them to guard against the threats in the cyber domain.
The Centre for Development of Advanced Computing (C-DAC) has developed this highly secure operating system. The system has successfully passed a crash test by the DRDO and Indian Army.
Re: Indian Cyber Warfare Discussion
Holding To Ransom
WannaCry malware attack raises questions for state, software producers, users
WannaCry malware attack raises questions for state, software producers, users
One curious aspect of WannaCry is that once it enters a computer, it tries to connect to a domain on the internet, and if it succeeds, it stops its activity. An alert cybersecurity researcher created that domain and helped slow WannaCry’s spread. Researchers are puzzled why this “killswitch” was left in the code. What’s worrisome is that perhaps a future variant of ransomware will try to send contents of the disk to a remote server before locking the computer, thereby stealing sensitive health or financial details, embarrassing photos or vital state secrets.
The targets may react to the ransom part of the attack and fail to see the data theft. This may have already happened. In response to an RTI, the RBI said that at least one bank was attacked by ransomware last year. If data-stealing malware targets computers in a corporate or government network, the real damage is not to the owners of the computers but the people whose data is exposed. In the case of government secrets, the entire country may be worse off.
Re: Indian Cyber Warfare Discussion
Hacked! Critical Data From UIDAI, BSE, RBI, ISRO Up For Sale On Darknet!
Pune based anti-virus provider Quickheal created ripples few hours ago, when they reported that critical data from more than 6000 establishments, businesses and organizations have been hacked, and put on sale on the darknet.
However, Govt. officials who are managing the entire Internet protocols in India have vehemently denied any such reports of data leak.
Quick Heal’s Enterprise Security brand Seqrite reported that they have witnessed an advertisement posted on the darknet, wherein the seller is offering crucial data from leading Govt. and private organizations for 15 bitcoins, which is approximately Rs 42 lakh.
Along with their partner seQtree InfoServices, they traced the advertiser, and dug out details regarding the offer, and the results are alarming. They even disguised as buyers, and contacted the advertisers for their services.
The hackers have claimed to disrupt business operations of any business they want, on demand. Maybe the amount of bitcoins charged would be even more for such ‘request’.
Seqrite has said, “This can be a major tool of mass disruption if a non-state actor gets hands on it,”
Some of the organizations which, as per Quickheal, are affected include: UIDAI (Aadhaar), Idea Telecom, Bombay Stock Exchange (BSE), Flipkart, DRDO, Aircel, Reserve Bank of India, BSNL, SBI, TCS, ISRO, ICICI Prudential Mutual Fund, VMWare, Employees’ Provident Fund Organization, various Indian state government portals, and others.